Antivirus And Security
How to remove viruses or malware?
When talking about malware it refers to any type of malicious software that tries to infect a computer or mobile device. Hackers use malware for several reasons. Such as extracting personal information or passwords, stealing money, or preventing owners from accessing your device. ‘Malware’ is a general term used to refer to a variety of types of intrusive software. And that in most cases they are used with a malicious end. Here we will see how to remove viruses.
It is not always easy to know if pc is compromised or not, because nowadays cyber criminals make great efforts to hide the code and hide what their programs are doing on the infected computer. Therefore it is very difficult to provide a list of symptoms characteristic of an infected pc. And that’s because the same symptoms can also be caused by hardware incompatibilities or system instability, however, here are just a few examples that may suggest that your PC has been compromised:
- You may receive the error “Internet Explorer could not display the page” when trying to access certain websites.
- Your web browser (e.g., Microsoft Internet Explorer, Mozilla Firefox, Google Chrome) becomes blocked, hangs, or unresponsive.
- The default home page of your web browser is changed for no reason.
- You are redirected to web pages other than the one you intended to visit.
- You receive numerous web browser pop-ups (popups)
- Strange or unexpected toolbars appear at the top of your web browser
- Your computer runs slower than normal
- Your computer hangs hangs, hangs, or is unresponsive
- There are new icons on your desktop that you don’t recognize
- Your computer restarts on its own (but not a restart caused by Windows updates)
- You will see unusual error messages (for example, messages that indicate that corrupted folders or files are missing)
- You cannot access Control Panel, Task Manager, Registry Editor, or Command Prompt.
Within the malware is included viruses, ransomware, worms, Trojans, rootkits, keyloggers, dialers, spyware, adware,rogue security software and other malicious programs; most active malware threats are usually worms or Trojans rather than viruses.
Below you can find a brief description of the types of malware that can be found the most:
- Trojans
Trojan is a type of malware that pretends to be something useful and fun while causing damage or data theft. Trojans often silently download other malware (e.g. spyware, adware, ransomware) onto an infected device as well. - worm
A computer worm is a type of Trojan capable of spreading or replicating from one system to another. You can do this in several ways. Unlike viruses, worms do not need a host file to hook up. After arriving and running on a target system, it may perform a number of malicious tasks, such as removing other malware, copying itself to devices physically connected to the affected system, deleting files, and consuming bandwidth. - spyware
Spyware is another type of malware with the peculiarity that it is very difficult to detect. It collects information about your browsing habits, browsing history or personal information (such as credit card numbers) and often uses the Internet to transmit this information to third parties without your knowledge. Keyloggers are a type of spyware that monitors your keystrokes. - ransomware
Ransomware is a threat that prevents users from accessing their system or personal files and demands a ransom payment to regain access to them. In many cases, even if you get to pay the ransom, your files/access are not returned to you. - Rootkits
The term “rootkit” comes from the “root kit”, a package that grants the highest privileges on the system. It is used to describe software that allows the stealth presence of unauthorized functionalities in the system. Rootkits modify and intercept typical modules of the environment (operating system). - adware
It is usually a standalone program that displays advertisements to the end user in a variety of ways: within the program itself, or via pop-ups, slither ads, browser pop-ups, embedded ads, or altered website content. The revenue generated by the ads is the way in which the program to which the adware is attached is paid, which means that the end user receives their desired tool or service “for free”.
To remove viruses, Trojans, worms, or other malware in Windows, follow these steps:
1. Enter safe mode
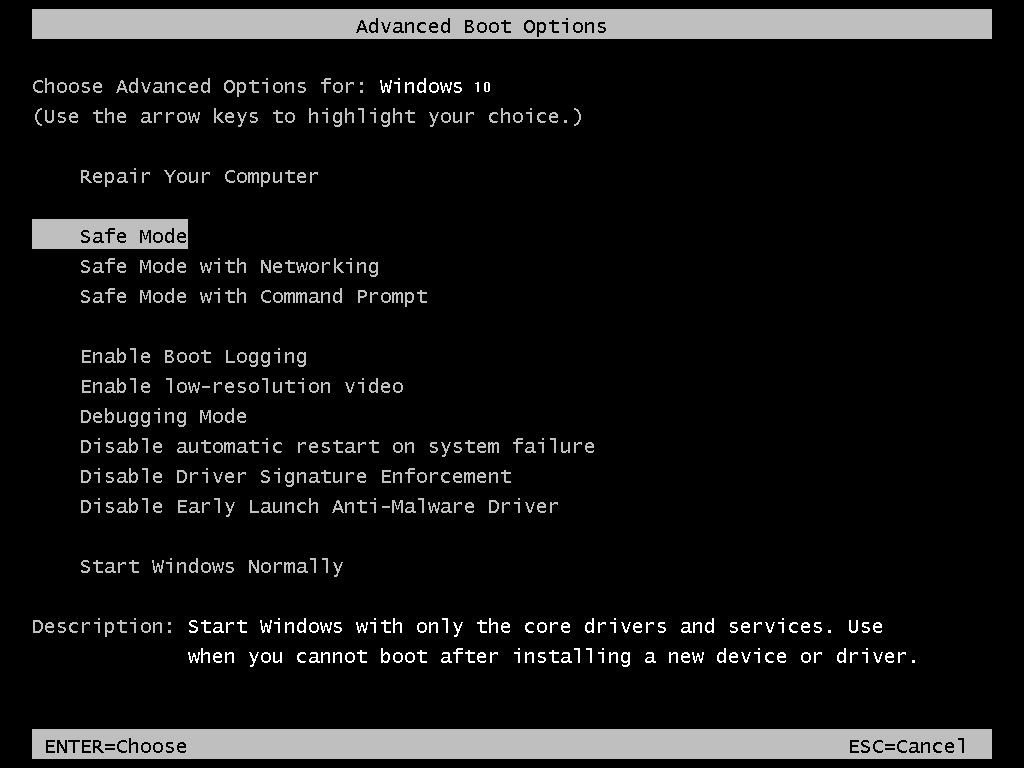
Some forms of malware may try to prevent you from using the tools below. If this happens, we recommend that you start your computer in safe mode with network connection and try from there to perform the Malwarebytes scan. Safe mode starts Windows in a basic state, using a limited set of files and drivers. So it can help you fix the problems on your PC as it is very likely that the virus will not load. To start your PC in safe mode with network, you can follow the steps below:
- When starting the computer, while booting you have to press the F8 key repeatedly until the menu appears. (photo)
- In the menu, choose the option “Safe Mode with Networking”.
2. Use Rkill to terminate suspicious programs
RKill is a program that will attempt to terminate all malicious processes associated with this infection, so that we can perform the next step without being interrupted by this malware.
Because this utility will only stop the malicious process and does not delete any files, it only removes viruses, after running it you should not restart your computer.
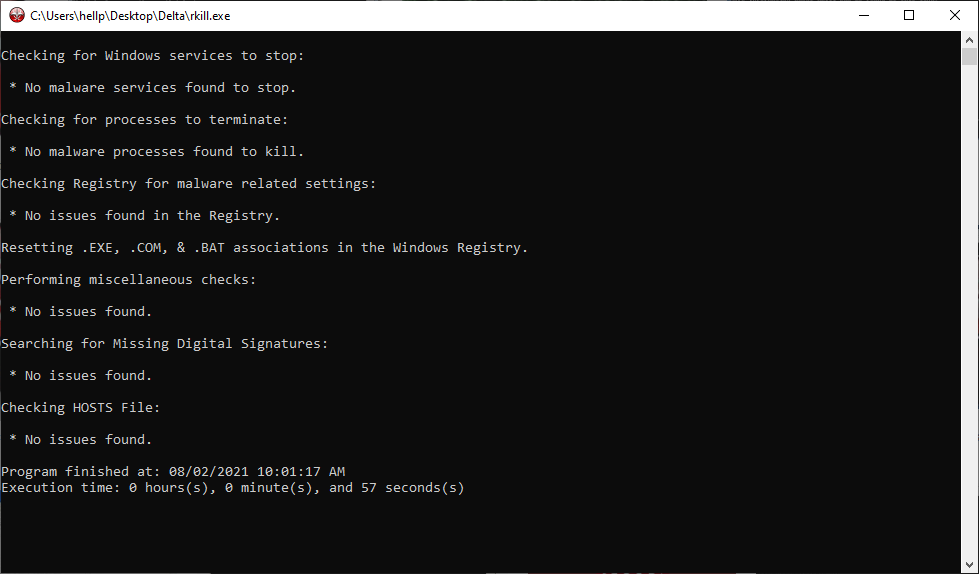
- You can download Rkill from the following link .
- Double-click the Rkill program to stop the execution of malicious programs.
- RKill will now start working in the background, be patient while this utility looks for malicious processes and tries to stop them.
- When the Rkill tool has completed its task, it will generate a log. Do not restart your computer after running RKill as the malicious programs will start again after the reset.
3. Use Malwarebytes to remove viruses, Trojans, worms or other malicious programs
- You can download Malwarebytes from the link below.
- When Malwarebytes has finished downloading, double-click the file to install Malwarebytes on your pc. You can skip a user account control pop-up window that asks if you want to allow Malwarebytes to make changes to your device. If this happens, you need to click “Yes” to continue with the installation.
- When you begin the malwarebytes installation, you will see the Malwarebytes Installation Wizard that will guide you through the installation process.
- To install Malwarebytes on your computer, follow the instructions by clicking on the “Next” button.
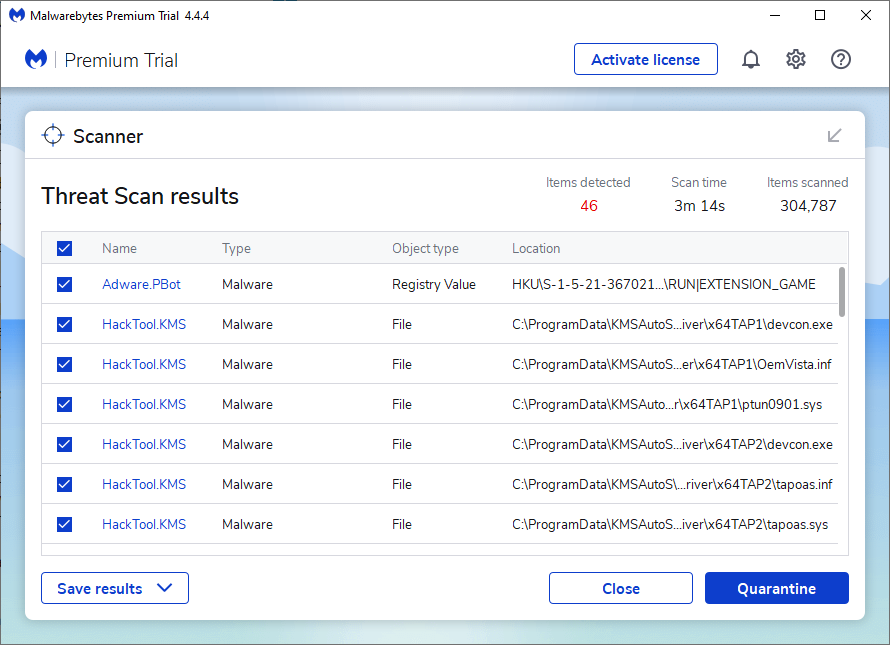
- Once installed, Malwarebytes will automatically start and update the anti-virus database. To start a system scan, you can click on the “Scan” button.
- Malwarebytes will start scanning your computer for malicious programs. This process can take minutes, so we suggest you do something else and periodically check the scan status.
- When the scanning is complete, you will be shown a screen showing the malware infections detected by Malwarebytes. To remove viruses that Malwarebytes has found, click on the button «Quarantine«.
- Malwarebytes will quarantine all malicious files and registry keys it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer. When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
4. HitmanPro to scan for malware and unwanted programs
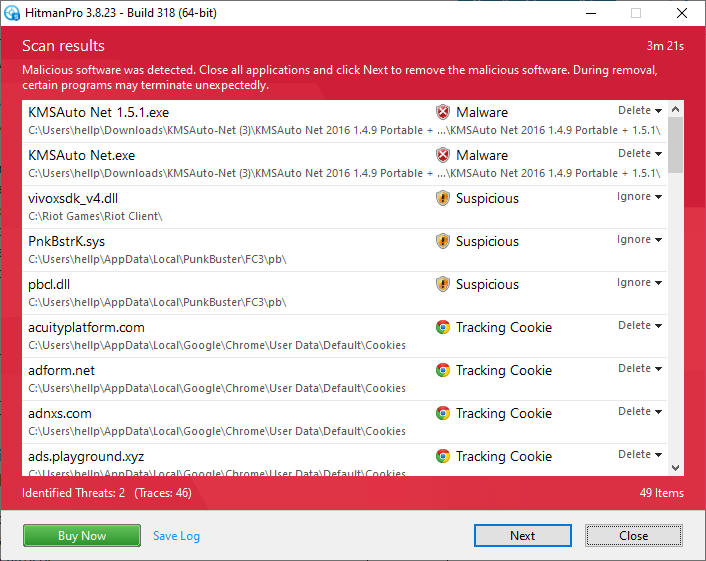
HitmanPro can find and remove viruses, malware, adware, bots and other threats that even the best antivirus package can bypass. HitmanPro is designed to work in conjunction with its suite of antivirus, firewall and other security tools.
- You can download HitmanPro from the link below.
- Install the program. A User Account Control pop-up window may appear asking if you want to allow HitmanPro to make changes to your device. If this happens, you need to click “Yes” to continue with the installation.
- When you launch the program, click the Next button to continue with the scanning process.
- When they are finished, it will display a list of all the malicious programs that the program found, as shown in the image. Click the “Next” button to remove viruses.
- Click the “Activate Free License” button to start the 30-day free trial and remove viruses. (it’s free)
- When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
5. Use Zemana AntiMalware Portable to remove Adware and Spyware viruses
Zemana AntiMalware Portable is a free utility that will scan your computer for adware, ransomsware and other malicious programs.
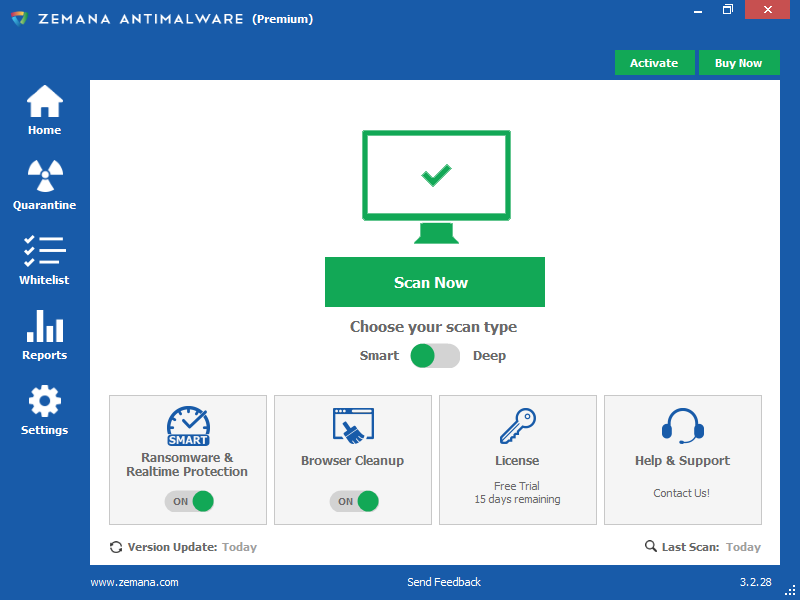
- You can download Zemana AntiMalware Portable from the following link .
- Double-click on the file named “Zemana.AntiMalware.Portable” to perform a system scan with Zemana AntiMalware Free.
- When Zemana AntiMalware starts, click the “Scan Now” button to perform a system scan.
- Zemana AntiMalware will now scan your computer for malicious programs. This process can take up to 10 minutes.
- When Zemana has finished scanning, it will display a screen showing any malware that has been detected. To remove all malicious files, click the “Apply Action” button.
- Zemana AntiMalware will now start removing viruses. When the process is complete, you can close Zemana AntiMalware.
6. Reset your browser to default settings
If you still have problems with adware in Internet Explorer, Firefox or Chrome, we will need to reset your browser to its default settings. This step should be performed only if your issues have not been resolved by the previous steps.
GOOGLE CHROME
Google Chrome has an option that will be reset to its default settings. Resetting your browser settings will reset unwanted changes caused by the installation of other programs. However, your saved bookmarks and passwords will not be deleted or modified.
1. Click the Chrome main menu button, represented by three horizontal lines. When the drop-down menu appears, select the option labeled Settings.
2. Chrome settings should now be displayed in a new tab or window, depending on your settings. Then scroll to the bottom of the page and click Advanced Settings.
3. Scroll down until the Reset Browser Settings section is visible. Then click the Reset Browser Settings button.
MOZILLA FIREFOX
If you’re having problems with Firefox, resetting it can be helpful. Many issues are fixed when restoring Firefox to its default state while saving its essential information such as bookmarks, passwords, autocomplete information web forms, browsing history, and open tabs.
1. Open firefox
2. Write in the address field as follows: about:support
3. Click “Reset Firefox” – top right.
With this should disappear most of the accumulated malware, in case the problem persists it is very likely that you have to get to format the computer (although there may be other solutions).




Peculiar article, just what I needed.